
Scam Bucket: Credit card fraud is inevitable
You can do everything right, but credit card fraud is inevitable.
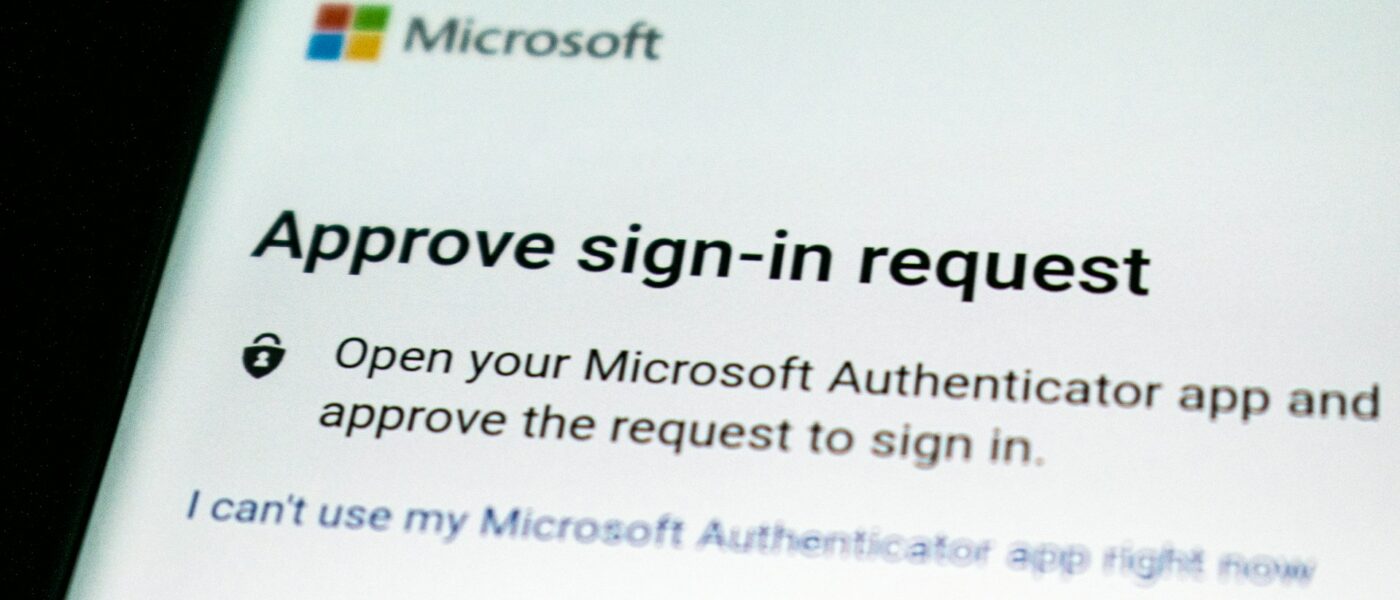
In recent weeks, Cyber Protection Magazine has fielded calls and emails from people who have followed all the best-known techniques for securing banking, debit, and credit card information. That includes bank notifications every time the card is used, multi-factor authentication (MFA), biometrics, and limiting the use of a card for specific transactions. These readers still experienced unauthorized use of their payment cards
How does that happen?
The market for criminal use of legitimate credit cards is a well-known “secret.” The most common sites are found on the DarkWeb, but occasionally they pop up on Meta sites, where they can reap thousands of dollars before Meta gets around to kicking them off, generally without prosecution.
The criminals collect most of this information through phishing attacks using email, but also on Facebook and Instagram, and falling for a phishing scam may negate victims’ claims they “did everything right.” Criminals, however, are getting more sophisticated. Enterprises selling the card information gather it by sending fraudulent emails or text messages, posing as legitimate entities, and tricking individuals into providing their credit card information. Then there is basic social engineering, manipulating victims into revealing their credit card information through phone calls, and QR codes.
Even more sophisticated, criminals will install skimming devices on ATMs, gas pumps, or point-of-sale terminals to capture credit card information when cards are swiped or inserted. While it may not be obvious that the skimmers have been added to the terminal, it is fairly easy to determine if it is legitimate. Legitimate card readers cannot be easily removed, while skimmers may be held on with a simple adhesive. Some locations, like Costco fueling stations, place tape over the reader and, if broken, can alert users and the vendor that there may have been a breach.
No one is completely safe
But by and large, data breaches are the most common source of stolen credit card information, and that is something most victims cannot do anything about.
By hacking into databases of companies or financial institutions criminals steal terabytes of credit card information. Employees of companies or financial institutions may access and sell credit card information, posting the information of those above, carding forums. Criminals exchange...
This content requires that you purchase additional access. The price is $1.00 or free for our Premium members.

Like Digital Cicadas, Cybercriminals Lie In Wait Before Unleashing Their Presence
A curious parallel can be drawn between cybercriminals and the intriguing phenomenon of Cicadas. Akin to the periodic insects that emerge from the ground after years of dormancy, cybercriminals often resurface with renewed vigor, unleashing their disruptive activities on unsuspecting organizations.
This content requires that you purchase additional access. The price is $1.00 or free for our Premium members.

Turning the corner on cyber insurance
It seems like the insurance industry is turning the corner on cyber insurance and making a decent profit in the process. But not every industry watcher is optimistic.
This content requires that you purchase additional access. The price is $1.00 or free for our Premium members.

Dissecting the Anatomy of Ransomware
Most people understand by now the impact that ransomware can have on their systems if infected. But what precedes this critical point? Is the deployment of ransomware a gradual process, or does it occur in a single, quick action? Ransomware…...

How serious do companies take cybersecurity?
Cybersecurity in an organisation is primarily a proactive effort. Whilst it does have a reactive component as well, a response to a cyberattack may only be successful with proper planning and preparation. The hope with a crisis response plan is…...
This content requires that you purchase additional access. The price is $1.00 or free for our Premium members.
The Era of AI-Powered Cyberthreats?
From our predictions issue: AI is rapidly infiltrating the business world and our daily lives. While revolutionizing how – and how efficiently – work gets done, it also introduces a new set of cybersecurity challenges.
You must first purchase a membership level before purchasing this content.

Breach affects half of France
French regulators recently warned that a January 2024 cyber-attack on two major healthcare sector companies caused over 33 million people’s data to be compromised. The data includes sensitive personal information, which threat actors could exploit in phishing campaigns and financial…...
Cyber Threats Impacting Enterprises in 2024
From our predictions issue: With the new year, CIOs must educate and prepare themselves for the upcoming obstacles they may face in the future and implement ways to stay ahead and double down to protect themselves and their clients from potential vulnerabilities.
This content requires that you purchase additional access. The price is $1.00 or free for our Premium members.

Tracking 2024’s top three cybersecurity threats
From our predictions issue: As 2024 gets underway, here are three threats which promise to be making waves in the coming year.

Report: 2024 Threat Landscape
From our predictions issue: The cybersecurity landscape in 2024 is poised for significant developments and challenges. This report offers valuable insights into the evolving threat landscape and the measures needed to mitigate risks effectively.
Cyber Security in 2024
In an environment where the variety of cyber security attack strategies continues to cause major concerns, understanding what might be in store for security leaders and their teams next year is a complex challenge.
Safer Internet Day: Cybersecurity Best Practices
Safer Internet Day aims to raise awareness among young people of online issues. But they’re not the only ones who need to be aware of online safety. Businesses are just as vulnerable to cyber threats if they don’t protect themselves appropriately.
Experts leery of “benefits” of AI
Generative AI platforms have dominated news cycles for much of 2023 and that probably won’t abate in 2024. That isn’t surprising. The technology is spreading through every facet of life. Our lead article from the 2024 predictions issue!

2024: The year of GenAI
From our predictions issue: With ChatGPT the discussion around generative AI continues. But, beyond the headlines, what are the security implications? Can GenAI ever be used by professionals working in the security space?
Five critical cybersecurity trends for 2024
As companies make cybersecurity a core focus going into 2024, cybercriminals are adapting by developing sophisticated social engineering tactics, using AI to launch more effective attacks, and targeting new attack vectors.
How end-to-encryption can protect businesses from the increased risks of ChatGPT
As the use of AI continues to grow in the business world, so too do the risks of cybercriminals exploiting these technologies for their own gain. One such threat comes from generative AI tools like ChatGPT, which can be used by hackers to penetrate corporate systems and disrupt business operations.

ChatGPT One Year On: The good, the bad and the unknown
In celebration of the technology’s first year, we spoke to six security experts about the good, the bad and the unknown of generative AI to determine what the next year of ChatGPT’s life could have in store.
The #1 Way to Protect Against Cybersecurity’s Primary Threat Surface
A strong foundation of multi-layered email security is the best way to protect email servers and user inboxes from a disastrous breach.

Navigating the Digital Battleground – Expert Voices on Cybersecurity Awareness Month
As October is coming to an end with eerie Halloween celebrations, we’d like to remind everyone that today also marks the last day of National Cybersecurity Awareness Month.

The Big Cybersecurity Error Companies Make and Four Steps To Correct It
Staying ahead of complacency requires a multi-faceted approach— there are four steps organizations need to take.


