API Security is the New Application Security
APIs are rapidly evolving into much more than just a technological infrastructure, becoming the new application layer. It is good news for modern enterprises, primarily because APIs facilitate value delivery in new ways, quickly emerging an integral part of innovative business models and value creation for partners and customers.
Enterprises love APIs
According to a recent survey conducted by Imvision, the importance of API Security continues to grow. Today, more than 71% of large enterprises already use more than 50 APIs, with 80% of these enterprises publish APIs for either partners or clients. However, more API developments come with new types of vulnerabilities and expanded attack surfaces.
One key finding is that API Security is now a top priority among contemporary security leaders. Statistics indicate that more than 91% of security leaders intend to make API Security a priority over the next year, while 80% aim to gain more control over their APIs. Only a third of security leaders think their APIs attain the protection required.
The study reveals that APIs pose new challenges and security risks, challenging security leaders to rethink their approach to application security and to approach these new challenges is through cross-team collaboration.
The API Security Backbone
Another main finding is the strong push for an ‘API Security Backbone’ we witness among modern enterprises. Security leaders prioritize access control, security testing, and runtime protection as the main components needed for robust API security program. In this context, integration with existing organizational systems and gaining visibility are seen as the top critical enablers for successful implementation of API security.
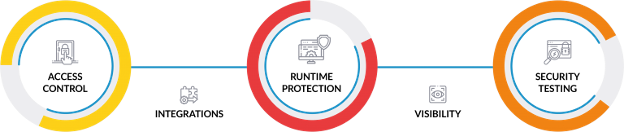
It is essential to note that every API is unique in terms of technologies and responsibilities. In light of this, there is a need for all different security components to work effectively around the attack surface that is particular API. It is now clear that critical elements of API Security need to be implemented effectively if an organization is to attain a robust security foundation.
The API Management (APIM) platform is a widely used technology that supports API Security, with more than 80% of the enterprises already using or planning to use it. An APIM platform handles Access Control and provides some Runtime Protection as a component of the API Gateway, primarily volumetric protection and basic policies when it comes to enforcing the API schema. It offers little to no cover for advanced API abuses and functional attacks. Additionally, it guarantees no support for security testing.
Your WAF is not enough
Despite turning the wheels of customer satisfaction and innovation and being relatively easy to use, it isn’t easy to build, maintain and secure APIs. Some security professionals may be tempted to think that the many layers of data, network, cloud and application protection ate enough to cover their APIs. But in reality, this is not the case since every API has its unique functionality, making it vulnerable to functional attacks that have no signature that exploits unique design and application defects.
Existing general-purpose security solutions have gaps that compromise the ability to identify irregular usage by unauthenticated users effectively. In fact, according to security experts, protecting web APIs with traditional application security tools alone is ineffective. More than 50% of security leaders commented that general-purpose application security tools, like WAF and SAST/DAST, are not on their roadmap for API Security.

Access Control capabilities can be hindered by the inability to alert in case of abnormal field usage. In the context of Runtime Protection, these gaps reduce the APIs ability to guarantee protection from unique vulnerabilities. In this case, the problem lies in the inability to learn the application context to detect anomalies. Security Testing is also compromised when the API cannot perceive the business logic. Ultimately, this reduces the ability to prevent attacks that manipulate the functionality.
With the expansion of the attack surface, many organizations recognize that their current tools are limited, but there is no viable alternative. Accordingly, this creates a need for new technologies for security testing and runtime protection to complement the APIM as part of the API security backbone.
Collaboration is the best medicine
The survey findings indicate that centralized integration teams are the go-to option for enterprises when it comes to handling API security. These integration teams can assume the form of dedicated API teams, centers of excellence or other entities.
While these teams typically operate the APIM platform, security leaders actually maintain that they should be responsible for API security. 42% of security leaders believe the security team should be in charge of API security, while in reality only in 28% of organizations this is the case.
This key finding exposes the challenge of responsibility that underlies enterprise API security. Addressing this issue requires collaboration to leverage the experience of traditional enterprise security areas, combined with deep understanding of the unique challenges presented by the nature of APIs.
The lack of a clear guiding framework for organizations in the context of API security reinforces the need for collaboration. Indeed, cooperation is an essential factor in helping enterprises achieve the ideal API security backbone.
Helping enterprises open up without being vulnerable




Pingback: Possession Of The API Safety Lifecycle - Hostor Infotech %
Pingback: Ownership Of The API Security Lifecycle - Gadget News Hub
Pingback: Ownership Of The API Security Lifecycle – OasisNews
Pingback: Ownership Of The API Security Lifecycle – Krypto Tech Lens