Haven free AI Security Companion protects from phishing
New AI-powered protection analyzes the context behind emails and browser activity to help users spot threats that traditional filters miss.
What Every SMB Needs To Know About Cloud Security
Today’s small and growing businesses run on the cloud, from invoicing and CRM to collaboration and communication. But as cloud adoption accelerates, so does the…
From Patch Fatigue to Boardroom Risk: Cybersecurity’s Reckoning Has Begun
In today's organizational cybersecurity initiatives, incremental change is no longer enough. Bad actors are too organized and focused on using sophisticated AI-driven attacks that shred…
In the Age of AI Coding, Software Architecture Matters More Than Ever
Artificial intelligence (AI) has had everyone agog with the possibility of replacing engineers and putting software creation in the hands of non-developers. Everyone is talking…
World Backup Day: The New Reality of Data Resilience
Ransomware has evolved; attackers now hunt for backup systems before launching the main strike. They slip into an environment, corrupt the recovery chain, then trigger…
Detecting Dangling SaaS Subdomains and Real Subdomain Takeovers
Subdomain takeover is one of those vulnerabilities that refuses to die. Every few years it gets rediscovered, scanners add more signatures, and reports get louder,…
DROP drops for consumer privacy
California this year launched an online site to put teeth into the 2023 California Delete Act. It could be the most powerful privacy tool consumers…
Pig butchering: Proving the Luddites right
Pig-butchering may be proving the Luddites were right. The social-engineering scam bypassed ransomware as the most profitable cybercrime approximately two years ago. After government regulations…
Turning the corner on cyber insurance
It seems like the insurance industry is turning the corner on cyber insurance and making a decent profit in the process. But not every industry…
Opinion: Deprioritize social media for peace
Finding content from legacy media is getting difficult in social media by design of the management of social media companies, while information from radicalized groups,…
7 Most Dangerous Cybersecurity Threats
In the ever-evolving landscape of technology, each year brings a new set of cybersecurity threats that can put your digital life and sensitive information at…
From Coders to Protectors: Women’s Influence in Cybersecurity
The need for knowledgeable people to safeguard our online environment has increased. In this context, women have become significant influences in cybersecurity.
Support Us
How about you buy us a coffee?
Newsletter
Read our archived Newsletters here.
Voices in Cybersecurity
Podcast
Hollywood strikes fight over ownership of biometrics
Everybody is going to own their own data. I'm going to own my own data. You going to own your own data. Your mother, your…
How companies are helping customers take responsibility for security
The goal of these companies is to make the job of protecting user data easier for the user
Getting a handle on generative AI, before it gets a handle on us
No model if you stop at one and two is of any value unless it can sort out whether the information sources that it's actually…
What’s up with TikTok
TikTok is like a Dickens novel. It’s the best of apps. It’s the worst of apps. There seems to be no in-between. Over the next…
Data removal services face uphill battle in healthcare
The data broker market is worth half a trillion dollars and growing at a rate of 7.3 percent annually through 2033. That means they don’t care that you want your privacy. They are making too much money selling your personal…
Latest Video
Know-How
Scam Bucket: Think before you click unsubscribe
You’ve done this many times. Checking your email you find a ton of spam, especially from this one organization or person. You are finally tired…
Poor marketing endangers society
n the past few weeks, as various security companies have published multiple studies about the state of cybersecurity, a common theme has arisen: Executives running…
Scam Bucket: Innocence is no replacement for digital vigilance
On Mastodon a poster asked last week, “Looking for an article or blog or text, that succinctly describes, at grade 1 level English, why ‘if…
Elder fraud festers out of control
As legislatures around the world try to get a handle on the growth of ransomware, another category of cybercrime is festering out of control: Elder…
IAM in a shifting environment
The fourth annual Identity Management Day (April 9) brought the opportunity to assess and evaluate the shifting environment plaguing Identity and Access Management (IAM). Identity…
A lesson on election security from tea ladies
Our current election season faces the same problems as in 2016 and 2020. Foreign adversaries are interfering with the election process. This time we know…
Articles
Privacy Not Included Group dings Amazon this year
That doesn’t mean you shouldn’t buy those whizbang, nifty gifts this weekend, you just need to go into it knowing what you are unleashing upon…
Bolstering Workforce Security During Summer Holidays
While we all crave relaxed summer getaways, it’s crucial to understand that adversaries never go on vacation. Unlike in schoolsmore
Boosting digital hygiene without technology
When they discuss issues in meetings, we all agree on a passphrase for whatever decision maker is chosen. It’s not shared in emails, texts, or…
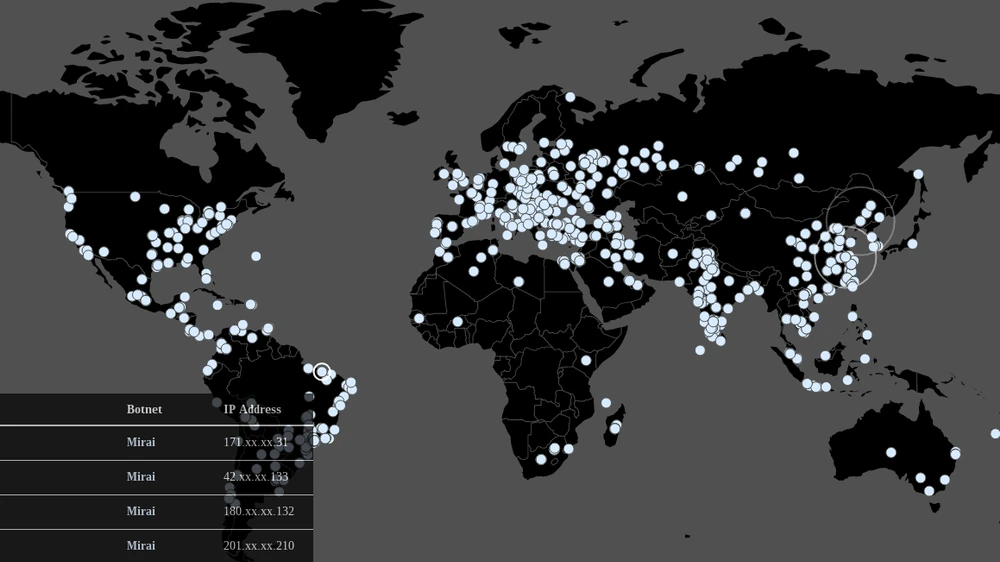
Protection against DDoS attacks: do’s and don’ts
The wave of DDoS attacks that flood the Internet daily made everyone aware of the relevance of tDDoS attacks. The question is how to properly…
Cheat Sheet: 3 Best Tips for Safer Internet Day
Today is Safer Internet Day and we thought we'd try a bit of click-baiting. That explains the headline and, coincidentally, also what this article is…
Scam Bucket: Microsoft reveals year-old Franken-phish campaign
Ever heard of Franken-phish? It's a campaign that targets Microsoft 365 users. It sells kits comprised of components of other kits readily available on the…
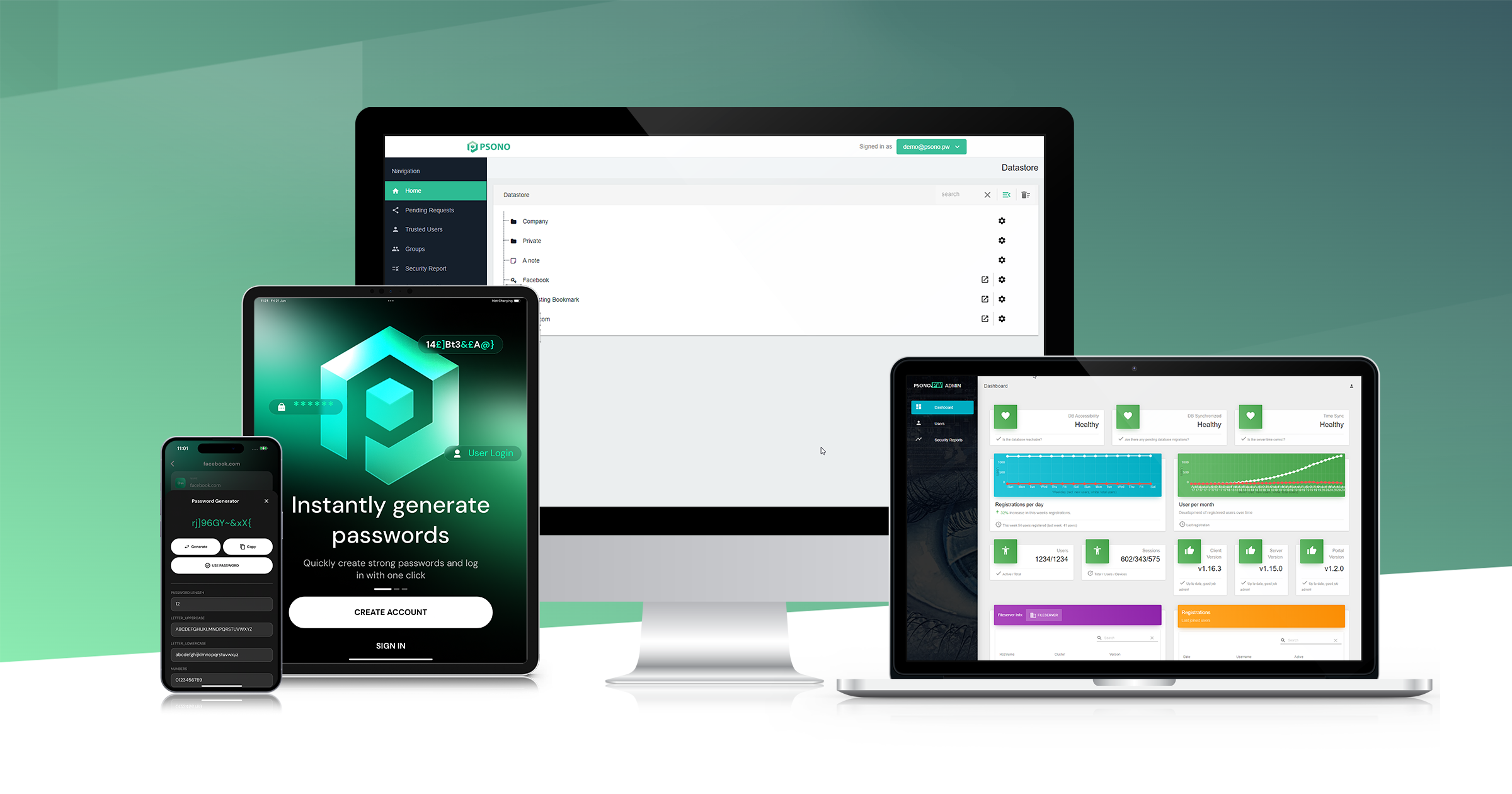
Cybersecurity companies tend to target large enterprises because, that’s where all the money is. supposedly. They may be missing a lucrative bet and a solution to AI-generated attacks. In 2025, Comcast issued a report that said 95% of all cyber breaches began with someone in an organization clicking on a…
Cloud-native application protection platforms (CNAPP) emerged as an industry niche around 2021, when Gartner coined the term to describe to consolidate cloud‑security capabilities under a single term. The niche evolved as organizations adopted cloud-native technologies and needed integrated security solutions. In short, CNAPP providers consolidate security and compliance into a…
The AI industry appears to be reaching a crossroads that will determine its future in the next two years. The only clear outcome is it will not be what it is now, nor what it is predicted to be. Most doomsayers and cheerleaders largely agree on a single vision: The…
Vibe coding (using LLMs to create computer code) was all the rage when 2025 began. By June, the bloom had fallen off the rose. Companies offering platforms and tools for the practice saw dramatic downturns in users. What happened? Evidence points to the traditional market practice of targeting early tech…
The Cybersecurity Information Sharing Act (CISA) of 2015 expired January 30, 2026. Whether that means anything is debatable. The 10-year old act facilitates sharing cyber threat information between the government and private sector organizations. Many security experts are unimpressed by how the act performed. Chaim Mazal, Chief AI and Security…
The Superbowl is a few days away, the Winter Olympics starts in February and the Summer Olympics is not far...more
As the world stumbles head on into deglobalization we predict national sovereign clouds will replace international access to data. That is good news for in-country corporations and for security companies in specific fields. It may not be so good for large multinational tech firms and people living in authoritarian countries.…
It’s that time of year when the weather turns cold, shoppers obsess over gift ideas, and tech companies start pounding the inbox with predictions for the next year. But for Cyber Protection Magazine we collect them all through December and compile them in January. Today we will look back and…
Happy Holidays - our last issue of the year is out, and it's all about Disinformation or, as we like to put it: Dysinformation. Dysinformation is a scourge of society, fueled by social media and malicious actors, but you may not have heard the term spelled this way. Dysinformation simply…
There has been a debate within the cybersecurity industry regarding cyber training effectiveness. On one side are tool providers who claim technology trumps training in securing data, networks, and people. On the other side is the $10-billion cyber training industry, growing at 20 percent per year. That says they must…
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.