Scam Bucket: Political/hate texts and what to do about them
Just when you thought the political fundraising texts were done, you get this screamer on your phone… Now that readsmore
Read more...
Just when you thought the political fundraising texts were done, you get this screamer on your phone… Now that readsmore
Read more...
It is Medicare scam season when Medicare patients can change their insurance plan for the new year, and that means………more...

On Mastodon a poster asked last week, “Looking for an article or blog or text, that succinctly describes, at grade 1 level English, why ‘if you have nothing to hide, you have nothing to fear’ is a crazy and bad argument, and perhaps also includes what some good arguments are.” We thought that is an excellent idea for a Scam Bucket post. Let’s get to the biggest argument against that philosophy.
It may not be scandalous, like a drug addiction, pornography or drug dealing, but there is personal information that everyone wants to keep from someone like passwords, account number and routing number to your bank account, and social security numbers
People who ascribe to the philosophy will readily agree to those limitations of what should be available to public knowledge. What they may not be willing to admit that they have done something in their life that they are ashamed. As Jesus Christ once proclaimed, “No one is without sin. No, not one.”
Sometimes, the error is made in ignorance. Clicking on a link in an email that connects to a porn site. Being rude to a waiter or failing to give a tip. Road rage someone recorded without knowledge or consent. Sometimes it was a mistake they made when they were younger and didn’t know any better… or knew better and did it anyway.
Then there are things that people are totally innocent of but were accused of it anyway. An average of 200–300 people are arrested every year for felonies but are exonerated, according to the National Registry of Exonerations. If the arrest was reported in the news, it is likely the exoneration was not. So the news of the arrest still exists even though they did not commit the crime.
John Gilmore, director of research at the data-scrubbing service DeleteMe, related a story of Jordan Greene, a journalist who covered neo-Nazi rally in North Carolina. Members of the group picked out his face in a photo of the rally, ran it through facial recognition, found where he lived and showed up at his house holding burning flares.
A recent scam has arisen ...
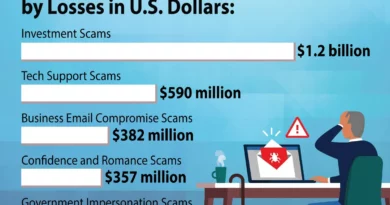
As legislatures around the world try to get a handle on the growth of ransomware, another category of cybercrime is festering out of control: Elder fraud.
The FBI’s Internet Crime Complaint Center (IC3) reported more than 100,000 people in the US, 60 years and older, lost $3.4 billion total to digital scams. The IC3 pointed out that the elderly are half as likely to report a loss. So the actual crimes and losses are probably much higher.
In contrast, the total ransomware payouts last year from reporting companies was $1.1 billion according to Chainanalysis. While the total number of fraud reports to the IC3 appears to have leveled off after years of growth, elder fraud increased by 14 percent year on year.
“Combatting the financial exploitation of those over 60 years of age continues to be a priority of the FBI,” wrote FBI Assistant Director Michael D. Nordwall, who leads the Bureau’s Criminal Investigative Division, in the report. “Along with our partners, we continually work to aid victims and to identify and investigate the individuals and criminal organizations that perpetrate these schemes and target the elderly.”
Who is vulnerable?

You can do everything right, but credit card fraud is inevitable.
In recent weeks, Cyber Protection Magazine has fielded calls and emails from people who have followed all the best-known techniques for securing banking, debit, and credit card information. That includes bank notifications every time the card is used, multi-factor authentication (MFA), biometrics, and limiting the use of a card for specific transactions. These readers still experienced unauthorized use of their payment cards
How does that happen?
The market for criminal use of legitimate credit cards is a well-known “secret.” The most common sites are found on the DarkWeb, but occasionally they pop up on Meta sites, where they can reap thousands of dollars before Meta gets around to kicking them off, generally without prosecution.
The criminals collect most of this information through phishing attacks using email, but also on Facebook and Instagram, and falling for a phishing scam may negate victims’ claims they “did everything right.” Criminals, however, are getting more sophisticated. Enterprises selling the card information gather it by sending fraudulent emails or text messages, posing as legitimate entities, and tricking individuals into providing their credit card information. Then there is basic social engineering, manipulating victims into revealing their credit card information through phone calls, and QR codes.
Even more sophisticated, criminals will install skimming devices on ATMs, gas pumps, or point-of-sale terminals to capture credit card information when cards are swiped or inserted. While it may not be obvious that the skimmers have been added to the terminal, it is fairly easy to determine if it is legitimate. Legitimate card readers cannot be easily removed, while skimmers may be held on with a simple adhesive. Some locations, like Costco fueling stations, place tape over the reader and, if broken, can alert users and the vendor that there may have been a breach.
No one is completely safe
But by and large, data breaches are the most common source of stolen credit card information, and that is something most victims cannot do anything about.
By hacking into databases of companies or financial institutions criminals steal terabytes of credit card information. Employees of companies or financial institutions may access and sell credit card information, posting the information of those above, carding forums. Criminals exchange...
“Brushing” scams are one of the rarer internet crimes and are hard to defend once started. They can range from relatively benign pranks to outright identity theft. Most commonly found on Amazon, they can occur on any e-commerce site that uses customer reviews to boost products.
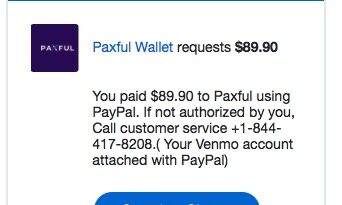
Ever heard of Paxful Wallet? If you’re one of the 3 million people who use it to buy, sell, and store cryptocurrency that answer is yes. Since that customer base represents less than one percent of the US population, probably not. Unless that is, you are one of the thousands more hit by the Paxful Wallet/Venmo Scam.
Read more...
A relatively new “smishing” attack (using SMS texts to gather personal information) is moving through the US, with the attackersmore
Read more...
Vishing, short for “voice phishing,” is on the rise again.…
Read more...
Cybercriminals are relentless, patient, and innovative. They take successful methods of scamming their victims and change them to make something new and even more effective. That’s what is making “hybrid vishing” a quickly growing threat.
Read more...