Not if, but when: Why it’s time to prepare for the quantum threat
In recent months, the drumbeat of warnings about the quantum security threat has reached an alarming crescendo.
In late November, the US Department of Commerce placed a dozen entities involved in quantum computing onto an export blacklist, fearing that they would help facilitate efforts to break US encryption and access classified data.
In the same month, Booz Allen Hamilton released a report underlining the urgency of the quantum threat. “Threat groups,” it read, will “soon collect encrypted data with long-term utility, expecting to eventually decrypt it with quantum computers.” The US National Security Agency, Department of Homeland Security, and National Counterintelligence and Security Center have also chimed in with their own warnings.
The message is clear: the encryption standards we rely on today are at serious and imminent risk thanks to quantum computers.
The threat to sensitive information
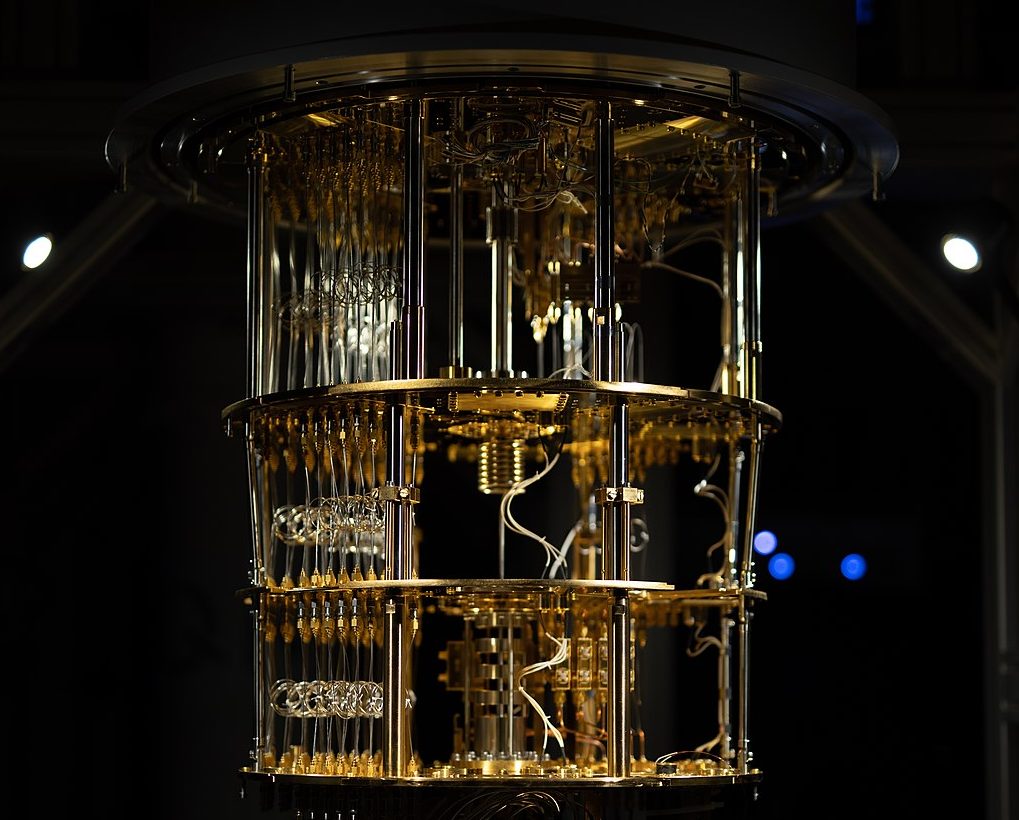
Today, virtually every organisation and device in the world relies on public-key cryptography vulnerable to the vast processing power of large-scale quantum computers, which – as proven by Shor’s algorithm – will easily be able to solve the mathematical problems underpinning it.
The result could be devastating, with everything from healthcare services to financial institutions exposed to the risk of digital signature forgery and data decryption.
Making matters worse is the fact that a quantum attack of this nature may be virtually undetectable when it happens. Threat groups and hostile states may already be harvesting encrypted data, then simply waiting for more powerful quantum computers to arrive before they can unlock it.
This is why the US National Security Agency has spent years warning about the quantum threat, as has the UK’s National Cyber Security Centre. As the US National Institute of Standards and Technology (NIST) notes, “nothing can be done to protect the confidentiality of encrypted material” once it’s stored by an adversary.
Mitigating the threat with a new standard for cryptography
In the middle of the last decade, NIST initiated a process to define new, quantum-ready cryptographic standards. Since then, it has been in the process of identifying post-quantum algorithms to replace current standards and establish a clear roadmap towards a quantum-secure future.
The current position of the NCSC and NSA is that the best defence is quantum‐safe cryptography underpinned by complex mathematical problems unaffected by Shor’s algorithm, implemented using classical computers and without specialist hardware.
Because the future capabilities of quantum computers remain an open question, NIST is pursuing a variety of mathematical approaches, each with different advantages and disadvantages in terms of practicality, implementation and design. Ultimately, NIST may choose to standardize multiple algorithms and hold another handful as backup options.
Either way, the publication of the final standards will trigger the biggest cryptography transition in decades.
Smoothing the path to quantum security
Though the final NIST standards may still be a way away, it’s possible for businesses to begin the transition to quantum readiness even before they’re announced.
The first step is to promote quantum literacy within your organisation to ensure that executive teams understand the severity and immediacy of the security threat. As the transition to full quantum-readiness is a serious undertaking, it’s only going to succeed if it has full support and investment from leadership.
As the Department of Homeland Security notes, the next step is to map out an inventory of all the systems using cryptography within your organisation and audit the security architecture and system design underpinning your technology stack. Data is at its most vulnerable when it is in transit, so be careful to map out all these weak points.
At the end of the process, you should have a list of systems which can or can’t be upgraded easily, a clear sense of your system’s vulnerabilities and areas of concern. From this position you can develop a phased plan for transition once the new post-quantum cryptographic standards are published. The French National Cybersecurity Agency (ANSSI) recently published a technical position paper outlining their recommendations for a phased hybridation to provide some post-quantum defence in the near term before the full transition to post-quantum cryptography.
For companies keen to protect themselves today, NIST has also suggested that certain cryptographic solutions combining finalist algorithms with existing public-key cryptography standards can be implemented in the transition phase, before full standards are announced.

Pingback: Planning for future threats - Cybersecurity