‘Tis the Season…for Cyberattacks!
Unlike the rest of us, cyber attackers don’t take vacations.
The holiday season is upon us, and many are preparing to celebrate with family and friends both near and far. For attackers, the holiday season is a perfect time to launch attacks, when businesses are closed or are operating with a skeletal crew. Furthermore, the continuing pandemic has heightened the threat, as many firms are operating with significant cybersecurity flaws resulting from the rapid shift to working from home.
Earlier this year, the FBI and Cybersecurity and Infrastructure Security Agency (CISA) published a joint advisory warning of an “increase in highly impactful ransomware attacks occurring on holidays and weekends — when offices are normally closed — in the United States.”
For example, the July 4 holiday weekend saw one of the single largest ransomware attacks to date, when an affiliate of the “REvil” cyber gang targeted software company Kaseya just six weeks after the Russian-linked cyber criminals sabotaged meat processor JBS over Memorial Day weekend, extorting the company for an $11 million ransom.
Colonial Pipeline paid a $4.4 million in ransom to the Russia-based hacking group DarkSide group after being forced to shut down its operations during Mother’s Day weekend (though the FBI later was able to recover $2.3 million of the ransom).
In 2021, the “everything shortage” is very real—and has left businesses, employees, and consumers at risk to cyber threats, especially supply chain and logistics, e-commerce and retail, and the travel industry. For example, the loss of manufacturing and logistics capacity, and employee-power in 2021 are expected to increase demand for goods, creating the perfect attack vector for cybercriminals: a potentially weak and vulnerable infrastructure that is easy to penetrate.
Let’s take a deeper look at some of the holiday-related malicious emails .
Thanksgiving, Black Friday, CyberMonday—a Lucrative Trifecta for Cyber Scammers
Consumers aren’t the only ones looking to take advantage of Black Friday and Cyber Monday. Cybercriminals are increasingly exploiting the holiday season to conduct spear-phishing campaigns and spread malware.
Thanksgiving Payroll Scam
The following sophisticated holiday scam is an interesting example. What happened?
Let’s take look at a recent case of a company that was impersonated. The email below allegedly displays an incoming fax message from the company to one the employees about payroll.
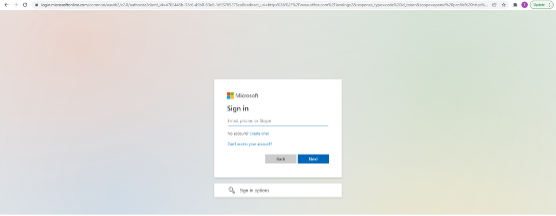
When the employee clicks on the link below, it redirects them to a spoofed but highly real-looking Microsoft login page. The attacker clearly did some reconnaissance beforehand to figure out which email exchange and domain the intended target used within the organization, in this case Microsoft 365.
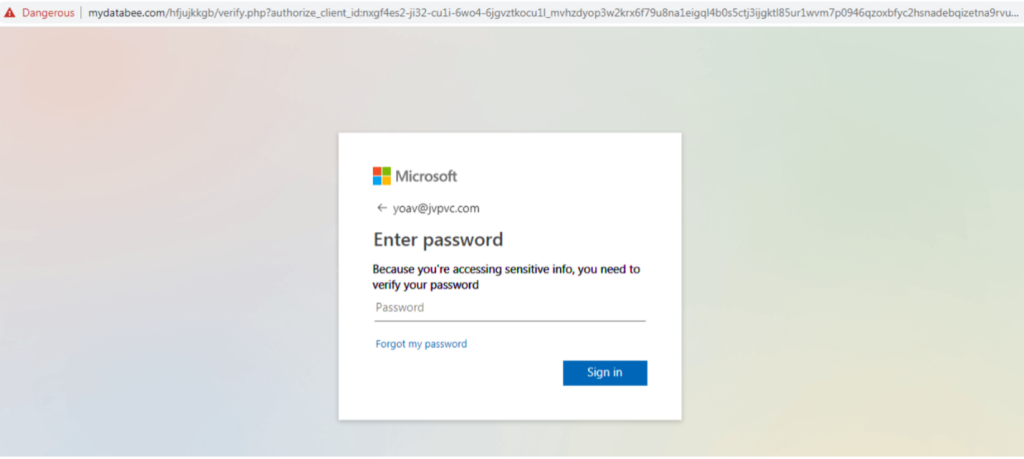
The spoofing of this login page is quite advanced—the logo is not pixelated, the “Forgot my Password” is clickable and redirects you to a real Microsoft reset password page. However, using image recognition, a good security tool could match authentic login pages against fake ones, and also detect that the sentence “Because you’re accessing sensitive info, you need to verify our password” is not the phrasing used in the authentic Microsoft login page. Furthermore, the URL of the page does not contain the company’s domain, but rather an unknown URL unrelated to the organization (see sceenshot above).
When you enter your password in the spoofed version, you get a message that the session has timed out.
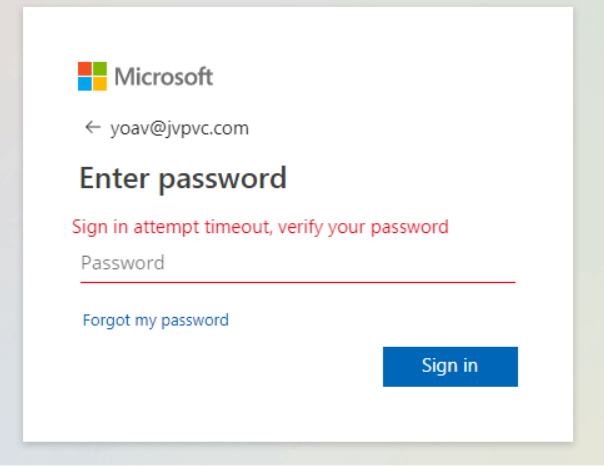
Again, both screens look extremely convincing, especially to the untrained eye. At this point, the attacker was able to harvest the intended target’s credentials and use them to gain entry to their email account, to conduct various malicious activities from a Business Email Compromise (BEC) attack, Account Takeover (ATO) and move laterally through the organization to gain access to critical data to extort ransom.
Black Friday Email Scams
In this scam, the intended target received a supposed complimentary gift voucher from Amazon.
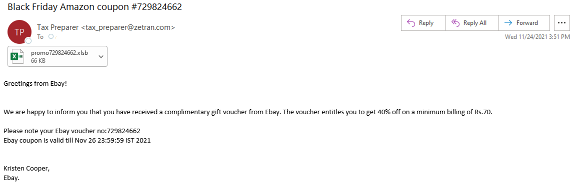
The goal is to get the intended target to download the Excel file with a malicious macro virus. Macro viruses, written in the same language as Excel and Word, can infect your documents, damage your computer software, and access your email account in order to send the virus to all your contacts. Just like in this example, macro viruses are usually spread through phishing emails.
Notice that:
- The subject of the email says the coupon from Amazon but in the body of the email it says it’s from eBay
- The sender is “Tax Preparer” and the reply-to email address is extremely long and does not match the domain of the sender, @zetran.com
- The amount is listed in Rupees
While it should be quite obvious that this email is malicious, unfortunately there are enough people who would open the email and download the file, letting cyber attackers into their networks.
Holiday Charity Scams
We saw a 500% increase in charity related scams from October through December. Cyber attackers exploit the fact that most people tend to be more charitable during the holiday season in order to launch cyberattacks. According to the FBI’s website, charity fraud rises during the holidays, when people choose to make end-of-year tax deductible gifts.
Business Email Compromise Holiday Scams
Business email compromise (BEC)—also known as email account compromise (EAC)—is one of the most financially damaging online crimes. It exploits the fact that so many of us rely on email to conduct business—both personal and professional. In a BEC scam, criminals send an email message that appears to come from a known source making a legitimate request.
Business owners, especially, should be extra vigilant to BEC attacks during the holiday season as increased transaction volumes can make it harder to spot suspicious activity. Similarly, if your company gives bonuses, the volume and dollar amount of these types of transactions could obscure a fraudulent payment unless someone is carefully checking accounts regularly. This time of year, many companies conduct benefit enrollment, end-of-year pay raises, or other changes that require communication to employees. Phishing emails that mimic these communications can result in someone gaining access to company data, passwords or other sensitive information.
Here are two more examples:
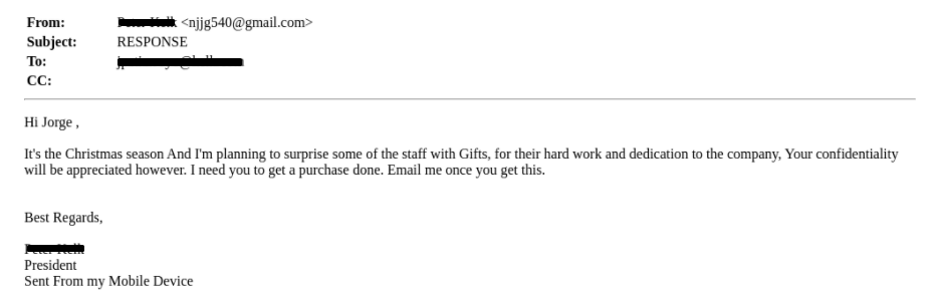
In this spearphishing email, a cyber attacker impersonating the president of the company asks another employee to help him purchase gifts for employees. This is a classic BEC scam where a spoofed email of a representative of the company is sent to employees asking them to perform an important task that could result in monetary and/or reputational risk.
Advanced-Fee Charity Scams
In this phishing email, the sender is supposedly the CEO of Walgreens Boots and claims that he is giving away 25% of his wealth to charity. All the intended target needs to do is respond to the email, in which case the attackers usually ask for a small up-front payment, which they claim will help them reach the large charity sum. This is otherwise known as an “advanced-fee” scam. There are many variations of this type of scam, including the “Nigerian prince” scam.
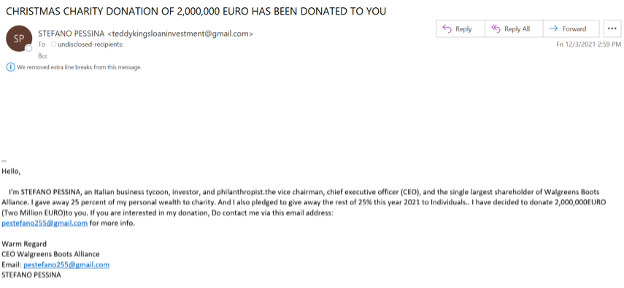
This holiday-related phishing email started to appear in October. A good email security services has rules that automatically flag emails with the words such as “money,” “CEO,” “investor”, etc. It should detect that the sender’s email does not match the reply-to email address listed in the body of the email.
Charity cyber scams exist in various forms and are an important reminder to us all to do thorough research before responding to an email, clicking on a URL, or donating any money.
Gift Card Scams Rampant During Holiday Season
In a lot of ways, gift cards are popular with cyber-criminals for the same reason they’re popular with consumers. They’re a near-ubiquitous store of money that can be used to buy a huge range of goods and services. According to the Federal Trade Commission’s Scam Alert, 40,000 people reported losing a whopping $148 million in gift cards to scammers during the first nine months of 2021, and this year could be the worst yet for such schemes as the global supply chain continues to face massive operational issues and gift card spending is expected to spike 27% (Blackhawk Network).
The following email was part of a “December Exclusive” campaign. Again, if the organization is using the right email security solution, the emails are automatically quarantined before they reach end-users for further investigation.
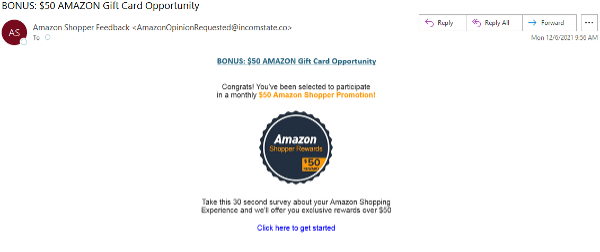

This is a popular tactic used by scammers to trick the intended target(s) into handing over their personal information. This is akin to a classic phishing attack, where the target is approached via email, text or social media with the offer of a large gift card balance. To claim it they need to fill in some personal and possibly financial details, which the scammer will then sell on the dark web or use themselves for identity fraud.
Don’t be Fooled by Fake Package Delivery Scams
We saw a monthly 47% increase from September to October, and a 25% increase from October to November in shipping and delivery related phishing scams. As more and more consumers are ordering online during this season (and overall due to the Covid-19 pandemic), so are many opportunistic scammers are targeting internet users by sending emails and text messages that impersonate delivery companies.
Here is a recent phishing example in which scammers impersonated FedEx. The email claims that the target needs to review the attached document in order to release the package from customs. What happens is that once the document is downloaded, a virus will be injected into the target’s computer.
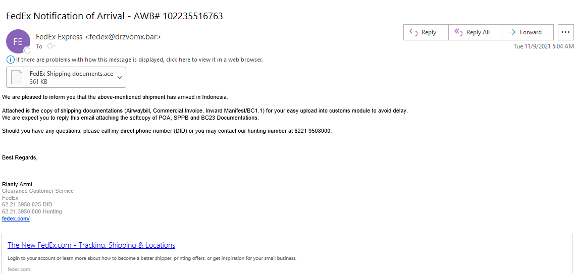
- Although FedEx is used in the sender’s display name, it’s not in the sender’s domain. We keep track of all the legitimate domains associated with FedEx (and other shipping companies) and this is not one of them.
- The file looks like an Adobe Acrobat file to the untrained eye, but this is an ‘execon’, which means the file runs an executable file.
- Upon further investigation of the domain, the website certificate was newly created and associated with other attempts at sending executable files.
- Within the body of the email, the scammer uses a common tactic to apply pressure on the target with language such as “if you don’t want a delay in delivery, you must download the form”.
- The scammer tried to make the email look more legitimate by putting the FedEx URL in their logo but didn’t include their email address as one usually does.
To wrap up…don’t be caught off guard this holiday season!
While fraud is a problem all year long, scammers are even more active around the holidays. They know consumers, and by extension, businesses, are stressed, distracted, and lacking in resources, especially this year, to protect themselves against cyber attacks and scam attempts.
During this time of year, to protect data and assets, both individuals and organizations need to be extremely vigilant and remember the following rule—cybersecurity attackers take advantage of relatively minor security lapses, such as a single user account controlled by a weak password or downloading an attachment from an unknown and unverified source, in order to launch enormously costly attacks.
Even though cybersecurity attackers will use the holidays to exploit unsuspecting victims, with enough preparation, vigilance and proactive protection, customers and brands can overcome security challenges during this season.
Motti is the VP of customer success and incident response at Perception Point. Motti's focus is on building sustainable customer relationships, ensuring the highest level of protection in the optimal way, and delivering the best customer experience in the market.
Prior to joining Perception Point, Motti served as senior sales engineer and as director of technology and new products at Red Bend (acquired for $250 million by Harman Kardon).


