Pig butchering: Proving the Luddites right
Pig-butchering may be proving the Luddites were right. The social-engineering scam bypassed ransomware as the most profitable cybercrime approximately two years ago. After government regulations and law enforcement took a big bite out of returns for ransomware this past year, public-private partnerships are taking aim at the new champ.
TL;DR
* Pig butchering eclipses losses from ransomware
* Top targets are tech savvy people under 50
* Human error trumps cyber awareness
* Public/private partnerships making inroads at dismantling scam operations
* Tips to avoid scams
* Podcast with Arkose CEO
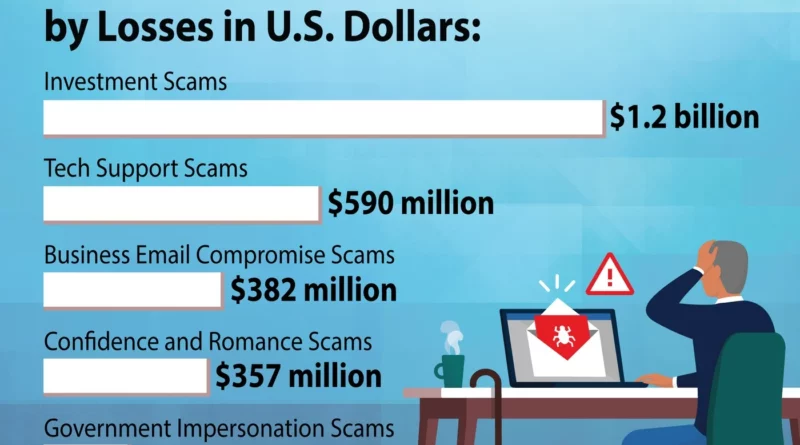
Between 2020 and 20023, scammers reaped more than $75 billion from victims around the world. Approximately 90 percent of the losses came from of purchasing fraudulent cryptocurrency, according to the US Treasury Department’s, Financial Crimes Enforcement Center. In comparison, ransomware attacks in that same period harvested $20 billion worldwide in ransoms and cost approximately another $20 billion in recovery costs.