What famous identity thefts can teach our businesses nowadays
There have been numerous cases of identity theft throughout history, some more famous than others. Who doesn’t know the story about the Romanov family and all the different girls claiming to be grand duchess Anastasia Nikolaevna of Russia, trying to steal her identity? While the techniques have changed throughout time, the truth is there is not much difference.
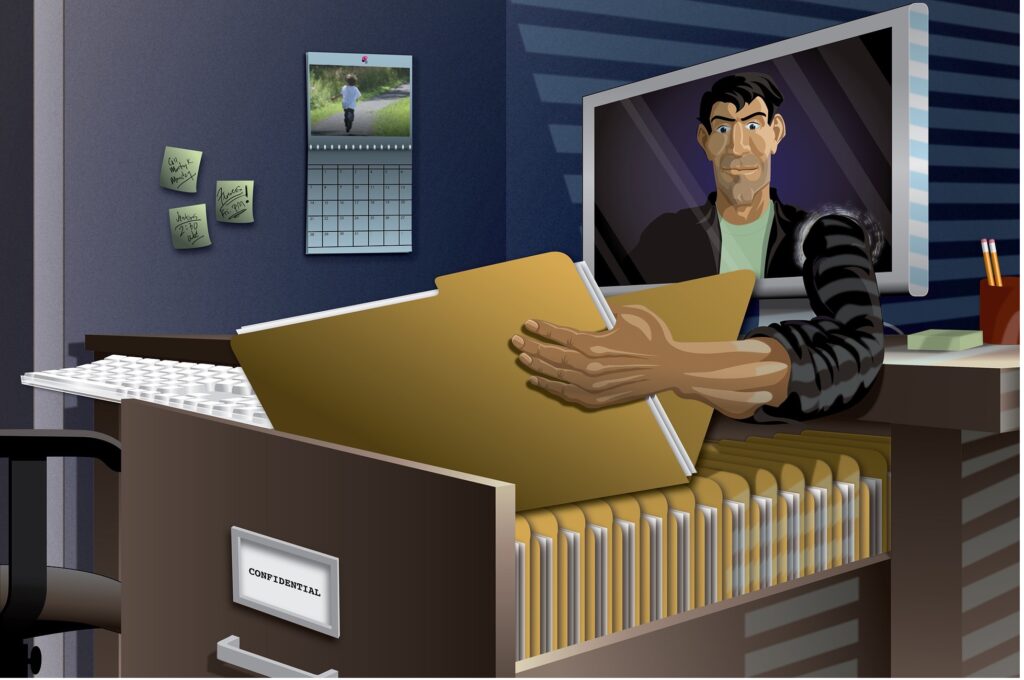
All that malicious actors and fraudsters need is to be convincing enough to persuade people to give them access to their confidential data. The only difference now is that they are no longer targeting individuals but also businesses whose databases allow them to reach even more people. According to a new Javelin Strategy & Research report, nearly 42 million Americans were impacted by identity thefts in 2021, resulting in $52 billion in total damages. With the increased use of the internet by individuals and companies and the new technological developments, the number will only continue to grow. Can we take a lesson from past identity thefts and learn how to protect ourselves today?
What is identity theft?
Before we learn what we can do to protect ourselves and our business, we first need to know what we are protecting against. What exactly is identity theft? Identity theft happens when someone gains access to your personal information and uses it for their gain without your consent. There are so many ways fraudsters can gain access to these details, through data breaches, phishing or business email compromise, social media quizzes, or even simple phone calls.
What can fraudsters do if they gain access to your sensitive data?
- Apply for new credit cards
- Apply for a loan or government support
- Use your payment details to make unauthorized purchases
- File fraudulent tax returns or health insurance claims
- Sell your confidential information on the darknet
- Access your bank account
- Take out loans in your name
As we can see, identity theft can have serious consequences, but the biggest issue is that in most cases, these attacks are not noticed soon enough, giving fraudsters more time for their malicious actions. Luckily, most cases of identity theft can be prevented by using common sense and starting to use technological advancements such as identity proofing for your benefit.
What are the most famous cases of identity theft?
While you can’t remove all possibilities of becoming a target of identity theft, you can significantly reduce the risk. By taking a lesson from history and using examples of famous cases of identity theft through history, you can start taking steps in the right direction. Discover how data can be stolen and what malicious actors can do with it, and you will be better prepared to protect your data and react quickly if the worst happens. Let’s go through some of the recent most famous identity theft cases that can help you determine what to do and, most importantly, what not to do.
1. Phillip Cummings case
One of the most famous and biggest cases of identity theft is the one of Phillip Cummings, who stole and sold credit reports from more than 30,000 people across the US. He worked in Teledata Communications, a credit reporting company that was working with more than 25,000 American companies.
Before leaving the company, he stole a spreadsheet with confidential passwords and codes that allowed them to access over 30,000 personal credit reports. They sold these reports to a network of fraudsters and criminals who used them for different malicious actions, resulting in between $50 million and $100 million in damages over three years.
2. Kenneth Gibson case
Kenneth Gibson worked for a software company where he had access to customers’ and employees’ personal information. He set up a computer program that would steal personal information data and automatically open fake accounts that he used to apply for linked credit accounts, creating more than 8,000 fraudulent PayPal accounts. He would then methodically transfer small amounts of money from those accounts adding up to $3.5 million in losses. Because he was moving small dollar amounts, his behavior didn’t raise red flags, making it easier to stay unnoticed, which is why he managed to do this for five years. In the end, he got caught because he became overconfident and reckless. Who knows how much longer he could continue with his malicious actions if he didn’t make a careless mistake?
3. Nakeisha Hall case
The Nakeisha Hall case proved that not even governments are safe against malicious actors and fraudsters. She worked for the IRS in the Taxpayer Advocate Services, where her duties were helping victims of tax fraud. This inspired her to try her own luck in fraudulent activities by using IRS databases to steal confidential data such as names, birth dates, and Social Security Numbers. With this information, Nakeisha would submit fraudulent tax returns and request refunds on debit cards, stealing around $400,000.
What can we learn from these examples?
These cases show how much damage just one person can do with the right kind of confidential information. In the last two years, 79% of organizations have experienced an identity-related security breach, which shows how important it is to start taking a proactive approach. Just imagine the consequences of Phillip Cummings case; not only did he cause significant damage to the business he worked in, but also their corporate clients and numerous individuals around the US. The biggest lesson from these three famous identity theft cases is to be careful with who you trust with your sensitive data. While it might be easier for all employees to have the same level of clearance, is that really necessary? The truth is that not all your employees need access to the same details; ensure that you have procedures in place that will regulate that.
Establishing security policies, conducting internal controls, and implementing safeguards that manage access to confidential information are essential for any company that wants to protect its business, employees, and clients. You have to be aware that often you can be in double danger when it comes to identity theft – fraudsters can steal confidential data from your business and exploit them, or they can use stolen data in your business. The results are the same; they are putting you in danger of chargeback requests and financial and reputational damage. To protect your business, it is essential to implement identity proofing and to authenticate a person’s identity before they can interact with your business, especially when making a purchase or submitting an application. By taking an extra security step of identity proofing, you are ensuring your customers are who they claim to be and significantly reducing the risk of your business becoming impacted by identity-related security breaches.
Conclusion
With our growing presence on the internet and companies undergoing digital transformation and transferring their business operations, the danger of identity theft is only becoming greater. Cybersecurity strategy is no longer an option for any company that has access to confidential information, regardless if the data is business, customer, or employee related. Combining common sense and educating your employees with security policies and the latest cybersecurity strategies will take you on the right way to ensure your business’s safety.



Pingback: Scam Bucket: Beware the ‘Unsubscribe’ button - Cyber Protection Magazine