How Criminals Attack the Building Blocks of the Internet
In the days of apps, web services, and cloud computing, where information and data are shared among many individual applications, APIs represent the building blocks. Without APIs, most company processes, especially across company borders, would not function properly. It’s therefore not a surprise that cyber criminals have identified APIs as one of the most lucrative targets when it comes to retrieving sensitive information. In an API security attack, the objective is mostly to exploit it for data or other malicious purposes.
There are many ways to attack API security. Some of the most common are SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF). Let’s have a look into each of those types of attacks and how you can prevent them.
- SQL Injection
An SQL injection is a type of API security attack which targets databases. It works by the attacker inserting malicious code into an SQL statement in order to gain access to data or to alter it for their own purposes.
Preventing SQL injection attacks is relatively simple. The easiest way to do this is to use parameterized queries. This is where placeholders are used for dynamic values, and the actual values are supplied when the query is executed. This ensures that the dynamic values cannot be interpreted as SQL code.
- Cross Site Scripting (XSS)
XSS is a similar type of attack, but instead of injecting malicious code into a database, XSS targets a web page or web application in order to steal user data or hijack their session. This is particularly dangerous since the user might be tricked into revealing sensitive information.
Some examples to prevent XSS include a web application firewall (WAF) that can detect and block XSS attacks. Another way is to use a content security policy (CSP) that can help prevent XSS attacks by specifying what content from what sources is allowed to be loaded by the browser.
- Cross-Site-Request-Forgery (CSRF)
An attacker forces an end user to execute unwanted actions on a web application. CSRF attacks target state-changing requests, not theft of data. With social engineering, an attacker may trick users into executing actions of the attacker’s choosing. If the victim is a normal user, a successful CSRF attack can force the user to perform state changing requests like transferring funds, changing their email address, and so forth. If the victim is an administrative account, CSRF can compromise the entire web application.
A good practice in preventing CSRF attacks is by including a token in all POST requests. The token should be unique to each user and should not be guessable. When a form is submitted, the token is compared to the one stored in the user’s session. If they don’t match, the request is rejected.
API security is critical
As can be seen from the examples above, API security is a critical issue for SMBs and enterprises that expose their API. Attacks on APIs can lead to data breaches, loss of customer trust, and reputation damage. Therefore, it is important to understand that these attacks can be prevented and mitigated.
Of course, depending on the specific details of the attack, there are various ways of mitigating the attack. However, some important which work for any attack and even protect your APIs better overall include:
- Using encryption and authentication measures
A common way is to use HTTPS with SSL/TLS. This will protect all communication between the client and the server. You can also use a digital certificate to prove that the server is who it says it is.
- Monitoring your API for suspicious activity
- Use a web application firewall (WAF) to monitor traffic and identify suspicious requests. However, be aware that WAFs require ongoing maintenance and regular updates.
- Use a log monitoring service to collect and analyze your API logs for anomalous activity.
- Responding quickly to any incidents
Cybersecurity is not only about detecting and identifying weaknesses and risks. Every organization needs to have a plan for what to do in case of an attack. This is also true for API attacks. Make sure you have a well-defined process in place to react to an incident.
- Good API documentation
To make sure that your API is well-documented, you can use auto-generated documentation tools, write clear and concise comments in your source code, or use a consistent name for your API elements. A good documentation will also ensure that developers understand how to properly use it. As a result, the risk of an attack which happens due to a misconfiguration will also be significantly reduced.
- Implementing rate limiting to prevent excessive or abusive requests
A good rate-limiting strategy for your API will depend on its specific needs and usage patterns. However, some common rate-limiting strategies include limiting the number of requests that can be made per unit of time, or per unit of data (e.g., per MB).
Protection can be achieved
As you can see, though APIs are increasingly attacked by cybercriminals, it’s pretty straightforward to prevent those attacks. Or at least make it as difficult as possible for the attacker. If you follow some basic principles in designing your API, both for the general development, but most importantly for some basic cybersecurity hygiene, you will go a long way in protecting your APIs. An online tool like the widget mentioned above will give you an even better security. We do recommend to establish solutions for business logic security testing into your development to ensure a smooth integration into your development processes. Besides that added layer of security, this will also make it easy for your developers to design their APIs securely right from the start – which, after all, is the best protection you can get.
BLST Security has made it possible to upload your JSON log file through an online widget and get results for free as shown in the following examples:
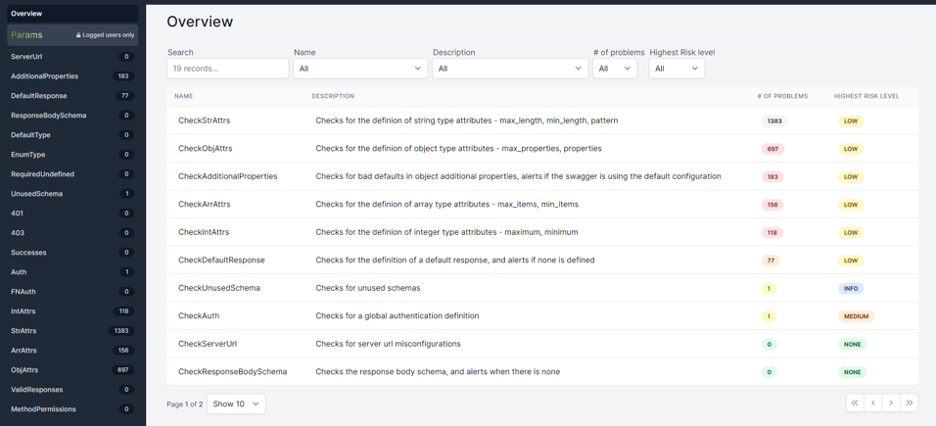
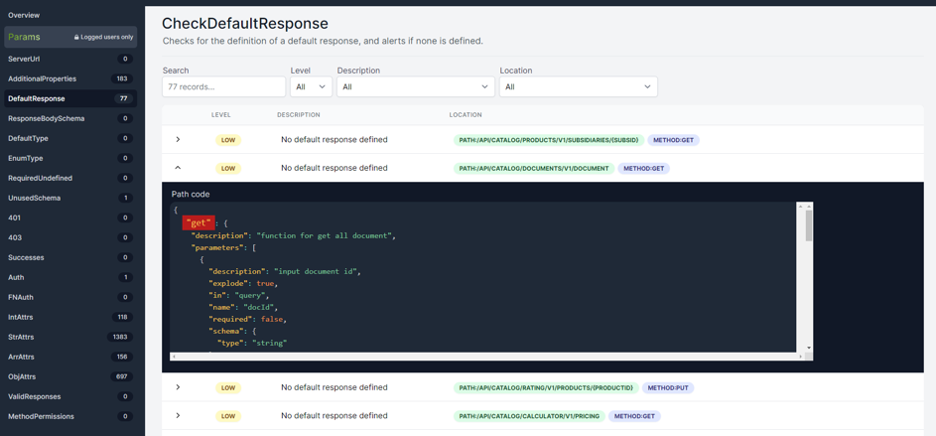
After a free signup, you can even view the Params table and have a deeper insight of your API.
BLST Security also offers API security testing service to scan your API for vulnerabilities that could be exploited by malicious actors.
Even better: you can even try the widget directly and right here
OpenAPI/Swagger Scanner
CEO at BLST Security, previously served as the head of a cybersecurity team in the Intelligence Corps in the Israeli Army, Chaim worked as a security architect of a virtual bank in Europe.


