Google at loggerheads over support for journalism
Google and the state of California have come to loggerheads over legislation designed to require Google to provide financial support for local journalism. Naturally, Google is fighting this with a PR and lobbying blitz. They and their allies may be missing the point. Whatever the outcome, it could have a profound impact on the democratic process. The legislation, The California Journalism Preservation Act (CJPA) has been wending its way through…

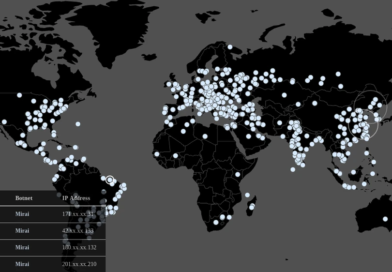
These are your 5 most dangerous devices
If you look around your house or office, you’ll be surprised which of your devices are the most risky. Spoiler: It’s not your computer.

Cybersecurity market heading for a reckoning
The cybersecurity market is heading for a reckoning without serious adjustments to marketing strategies. Recent reports, including one from Dimensional Research, showed large enterprises are planning significant cuts in budgets for security tools and services. Moreover, the vendors facing those

Unwanted Voice Traffic: A Growing Threat Impacts Businesses
A new report shows the growing threat of unwanted voice traffic and its pervasive impact on enterprises worldwide.

Is the way we recruit exacerbating the skills shortage?
The shortage in cybersecurity experts has led businesses to compete in earnest over a small pool of talent and the consequences of this are that more cybersecurity professionals are changing jobs than ever.
Features
Company News


Advertisement
Support Us
How about you buy us a coffee?
Newsletter
Read our archived Newsletters here.
Podcast

Murky third-party agreements weaken healthcare privacy controls
The healthcare industry is a vulnerable target of cybercriminals, but not for the reasons most business sectors are. Between 80 and 90 percent of all cybercrime results from people not following basic cyber hygiene practices, but in healthcare criminals gain access to information through infrastructure weaknesses and the murky third-party agreements.
Latest Video
Articles

Video Bytes: Changing the Script on Cybersecurity Hiring Part 2
t two of our video series with Matt Donato, managing director of #cybersecurity hiring company CyberSN, looks at strategies for discovering and communicating the actual personnel need for a company.

How Visibility Improves Security
If you want to know which devices in your network are insecure, you need to know your devices, all of them. In our latest Interview, Zac Warren from Tanium argues that visibility is key in achieving good security.

How Cybersecurity Businesses are Tackling the Ukraine War
The ongoing invasion of the Ukraine has raised concerns about an increase in cyber attacks around the world. We spoke with Morten Kjaersgaard, CEO of Helmdal Security, to give us his opinion on cyber attacks related to the Ukrain war and how it impacts global cybersecurity.
Guess what!? Today is World Backup Day
Backups will improve your resilience against cyber attacks. For today’s World Backup Day we have a special episode of our Crucial Tech podcast to highlight the importance of backing up your data.

Back it up: The basics of World Backup Day
It’s World Backup Day! To coincide with the day, Cyber Protection Magazine spoke to eight industry experts about the importance of backing up data and how to ensure that your backup is effective and can protect your data.

Video Byte: Changing the Script on Cybersecurity Hiring
Finding sufficient human and technology resources to protect company data has reached a crisis point. We explore hiring strategies and tactics with Matt Donato, managing director of CyberSN, in this latest Video Byte

How to protect personal data with technology
Personal identity information (PII) is more vulnerable than ever, so securing it becomes more important. CPM gives an overview of current and future solutions.
The Security Standard to rule them all
Taken from our latest special issue, Alex Leadbeater, ETSI’s Chair of Cybersecurity discusses their IoT-Security standard

Managing Cloud Security Costs
With an average annual cost averaging in the thousands per application, and with hundreds or thousands of applications in a cloud or hybrid cloud, cybersecurity costs can become expensive.
Fighting back against lateral attacks
Lateral attacks are a problem for the gaming industry, especially online games. Hackers use it not only to steal identities but to infiltrate corporate and government servers and steal proprietary data. Keeping attackers out is the primary goal of cybersecurity
Security Ideology Might be the Biggest Problem
Above strategy, there is something even more fundamental to the way security is carried out in organizations—ideology.