Editorial: Jog on, Meta
Mark Zuckerberg made two announcements about major changes in Meta in the past two weeks. The first was the revelation that they would be creating hundreds of AI-driven bots to interact with users. The second was the announcement that they would stop moderation of content, “except for dangerous stuff,” according to a video posted by Zuckerberg. With a certain amount of schadenfreude, we note that Meta had to pull the…
Why Zero Trust Should Be at the Heart of Every Organization’s Security Strategy
The Zero Trust approach treats every user and every access request in the system as a potential threat and approaches them with suspicion. This approach…
Cyber resilience needs action, not words, from world leaders
These days cybersecurity garners attention at the highest levels of government. But more decisive action is needed by world leaders to collectively strengthen defences globally,…
Cyberwarfare 2025: The Rise of AI Weapons, Zero-Days, and State-Sponsored Chaos
As we approach 2025, the notion of warfare is increasingly shifting from the physical to the digital domain. Cyberwarfare, once considered a supplementary tool for…
Command & Control: What You Should Know About Password Vulnerability
Organizations often find themselves in a continuous "chase," attempting to identify and neutralize the threat of exposed credentials before they are exploited.
Advertisement
Pig butchering: Proving the Luddites right
Pig-butchering may be proving the Luddites were right. The social-engineering scam bypassed ransomware as the most profitable cybercrime approximately two years ago. After government regulations…
Turning the corner on cyber insurance
It seems like the insurance industry is turning the corner on cyber insurance and making a decent profit in the process. But not every industry…
Opinion: Deprioritize social media for peace
Finding content from legacy media is getting difficult in social media by design of the management of social media companies, while information from radicalized groups,…
7 Most Dangerous Cybersecurity Threats
In the ever-evolving landscape of technology, each year brings a new set of cybersecurity threats that can put your digital life and sensitive information at…
From Coders to Protectors: Women’s Influence in Cybersecurity
The need for knowledgeable people to safeguard our online environment has increased. In this context, women have become significant influences in cybersecurity.
Support Us
How about you buy us a coffee?
Newsletter
Read our archived Newsletters here.
Voices in Cybersecurity
Podcast
Hollywood strikes fight over ownership of biometrics
Everybody is going to own their own data. I'm going to own my own data. You going to own your own data. Your mother, your…
How companies are helping customers take responsibility for security
The goal of these companies is to make the job of protecting user data easier for the user
Getting a handle on generative AI, before it gets a handle on us
No model if you stop at one and two is of any value unless it can sort out whether the information sources that it's actually…
What’s up with TikTok
TikTok is like a Dickens novel. It’s the best of apps. It’s the worst of apps. There seems to be no in-between. Over the next…
AI making life hard for consumers and cybersecurity
The AI industry supposedly to make life easier for humanity. Since it first burst onto the scene it has, arguably, made life more difficult. Consumers and the cybersecurity industry, in particular, are struggling professionally, emotionally, and mentally to understand the…
Latest Video
Know-How
Scam Bucket: Innocence is no replacement for digital vigilance
On Mastodon a poster asked last week, “Looking for an article or blog or text, that succinctly describes, at grade 1 level English, why ‘if…
Elder fraud festers out of control
As legislatures around the world try to get a handle on the growth of ransomware, another category of cybercrime is festering out of control: Elder…
IAM in a shifting environment
The fourth annual Identity Management Day (April 9) brought the opportunity to assess and evaluate the shifting environment plaguing Identity and Access Management (IAM). Identity…
A lesson on election security from tea ladies
Our current election season faces the same problems as in 2016 and 2020. Foreign adversaries are interfering with the election process. This time we know…
Privacy Not Included Group dings Amazon this year
That doesn’t mean you shouldn’t buy those whizbang, nifty gifts this weekend, you just need to go into it knowing what you are unleashing upon…
Bolstering Workforce Security During Summer Holidays
While we all crave relaxed summer getaways, it’s crucial to understand that adversaries never go on vacation. Unlike in schoolsmore
Articles
Boosting digital hygiene without technology
When they discuss issues in meetings, we all agree on a passphrase for whatever decision maker is chosen. It’s not shared in emails, texts, or…
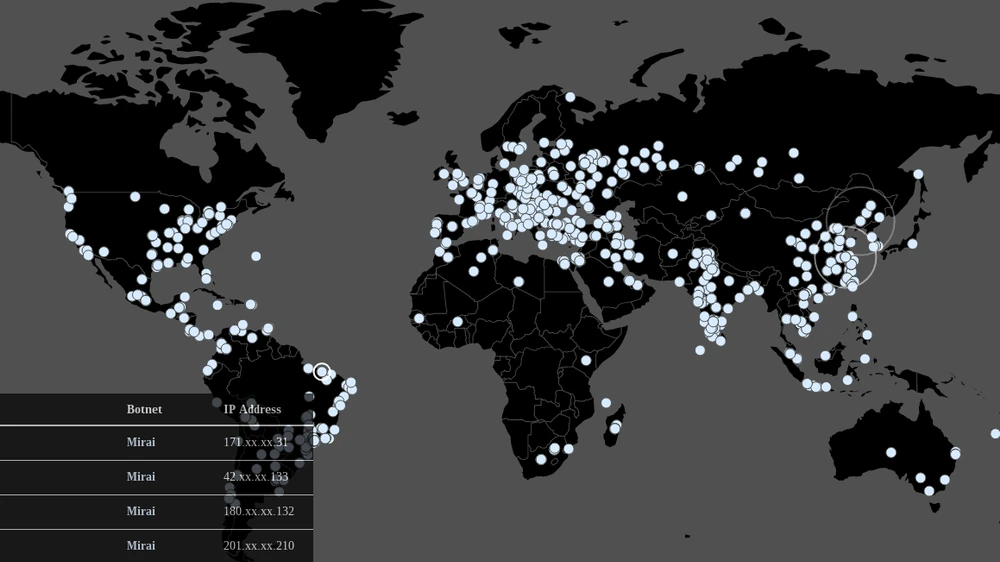
Protection against DDoS attacks: do’s and don’ts
The wave of DDoS attacks that flood the Internet daily made everyone aware of the relevance of tDDoS attacks. The question is how to properly…
Cheat Sheet: 3 Best Tips for Safer Internet Day
Today is Safer Internet Day and we thought we'd try a bit of click-baiting. That explains the headline and, coincidentally, also what this article is…
Scam Bucket: Microsoft reveals year-old Franken-phish campaign
Ever heard of Franken-phish? It's a campaign that targets Microsoft 365 users. It sells kits comprised of components of other kits readily available on the…
How Zero Trust supports IT and OT security
The recent ransomware attacks on critical infrastructure services could not have demonstrated more clearly how interwoven the IT environment is with the control of production…
Scam Bucket: Phishing, Smishing: It’s mostly Facebook’s fault
Smishing is the latest and growing version of phishing. In this case, it is using text messaging platforms to gather passwords and identities and deliver…
Just when you thought the political fundraising texts were done, you get this screamer on your phone… Now that readsmore
It is Medicare scam season when Medicare patients can change their insurance plan for the new year, and that means...more
n the past few weeks, as various security companies have published multiple studies about the state of cybersecurity, a common theme has arisen: Executives running the companies that purchase security tools and services are not sure their purchases have made them any safer. This widespread position in the market confirms…
t seems like everyone should be concerned, based on the level of urgency the companies present, but in the end, no one has yet built a quantum computer capable of breaking even the most standard 256-bit encryption. To that statement, the industry responds with, “Yet.” This year, however, the National…
There is a wide gap between regulatory compliance mandates and practical implementation and enforcement that I like to call the “Compliance Chasm”. That chasm is defined by the activity to protect consumers and consideration for the economic and operational impact on business enterprises. Finding that balance requires thought, not the…
Cybercrime reports flowing out of marketing departments still highlight the danger of ransomware. However, a closer look at the numbers reveals a much different story and poses the question: Have we reached peak ransomware? Last year, ransomware attacks hit all-time highs with paid ransoms exceeding $1.1 billion and attacks exceeding…
The Crowdstrike failure dominated the news this week and the debate is whether it is Crowdstrike’s or Miicrosoft’s fault. It...more
“Your security is important to us,” is a common phrase on corporate websites and emails, usually after some data breach that affects customers. To prove that statement, corporations invest billions of dollars in the cybersecurity industry. Most market projections say the industry is worth about $180 billion. About 15 percent…
Today businesses face increasingly sophisticated cyber threats that necessitate robust security measures. One such innovative approach gaining traction is the Security Operations Center as a Service (SOCaaS). This model offers organizations the opportunity to enhance their security operations efficiently and effectively by leveraging external expertise and advanced technologies.
When it comes to election security, the technology we use to vote and count those votes is not the problem. The problem is how naive we are. Election security has been at the forefront of daily news cycles for more a decade. The concerns about illicit use of technology to…